
Data breaches arguably constitute the gravest risk modern businesses face. According to an alarming report from the insurance company Hiscox, 70 percent of organizations are inadequately prepared for cyberattacks. This is particularly concerning in light of the multi-million, even billion dollar damages that can result from breaches. Already, far too many businesses have suffered devastating attacks; 45 percent of Hiscox’s poll respondents admitted to suffering at least one cyberattack in the past year, with many suffering two or more attacks.
At the small to midsize business level, cyberattacks aren’t merely annoying — they can spell certain doom for those already struggling to get by. Hence the need for robust security protocol. That’s exactly what the Center for Internet Security provides with its Top 20 list of Critical Security Controls. While these controls have been in the making for well over a decade, they’ve recently gained greater prominence at the federal and state level — and among private entities. Below, we offer an in-depth overview of this critical security tool, as well as suggestions for implementation:
What Are the CIS Top 20 Critical Security Controls?
The Center for Internet Security maintains detailed guidelines outlining prioritized actions known as critical security controls (CSCs). The goal is to proactively and effectively address security threats, thereby minimizing the potential for future data breaches. While any organization can benefit from implementing these controls, they are particularly valuable for those that currently lack robust security protocol. The CSC provide an accessible means of implementing security features while paving the path to a fully-fleshed compliance framework.
A Brief History of the CIS Top 20 CSC

Before diving in to explore specific controls, it helps to gain a broader understanding of how they came to be. They were initially developed in response to a 2008 request from the Office of the Secretary of Defense, in which assistance was sought from the National Security Agency. At the time, the NSA best understood the nature of cyber attacks — and how to combat them. Then, the White House maintained the following cybersecurity mantra: “Offense must inform defense.”
By the time the aforementioned request was made of the NSA, the agency had already compiled and refined a list of effective security controls dating back to the early 2000s. These controls were originally prompted by military requests. While the initial list was limited to official use, the NSA eventually agreed to share its compiled cybersecurity information in hopes of helping other government agencies improve their security protocol.
Upon validation by the U.S. State Department, the CIS Top 20 was found to align closely with thousands of documented attacks suffered at the federal level. In an effort to address significant security weaknesses, the State Department made integration of the CIS standards a clear priority. The effort was an undeniable success; the State Department achieved an impressive 88 percent reduction in risk across tens of thousands of systems. As a result, the CIS standards quickly became the blueprint of choice not only for other federal organizations, but also in the private sector.
Today, the CIS Top 20 controls are maintained and updated by a vast team of volunteers, including experts from every segment of the cyber ecosystem. Expert volunteers include auditors, threat analysts, policy-makers, users, and more. They come from a wide array of sectors, including everything from transportation to defense. Their feedback ensures that the controls remain not only effective for protecting against a range of security threats, but also accessible, scalable, and easy to implement for a broad spectrum of businesses and organizations.
Defining the Basic Controls (Top 6)
 Basic CIS Controls (click to enlarge)
Basic CIS Controls (click to enlarge)
The first six controls outlined by the CIS are often referred to as the ‘basic controls.’ While all of the outlined controls in the Top 20 are valuable, the basic CIS controls would ideally be implemented by all organizations seeking to ready themselves for future cyber attacks. Basic controls include the following:
#1 Inventory of Authorized and Unauthorized Hardware
It is imperative that organizations track all network devices — without a detailed inventory, it is virtually impossible to provide adequate protection. Successful application of the CIS first control is the foundation on which all other CIS controls rely. Putting this control into practice means identifying all relevant devices and maintaining a current inventory. This can be a huge undertaking; experts at CIS recommend using active scanning tools and other automated procedures.
#2 Inventory of Authorized and Unauthorized Software
This control references the need for active management of all network software to ensure that only authorized software is installed — and to quickly detect and deal with any unauthorized software that finds its way into managed networks. Cybercriminals regard organizations with vulnerable software as easy targets. Organizations that identify all existing software and develop approved whitelists improve visibility and may even see considerable savings as they discard unnecessary programs.
#3 Continuous Vulnerability Management
From software updates and patches to threat bulletins, ample opportunities exist for attackers to take advantage of new vulnerabilities — even among systems initially designed to be secure. As new vulnerabilities are reported, would-be attackers race to exploit these gaps. Without continuous scanning, organizations risk falling behind — a huge threat given the common knowledge that time is of the essence in the event of an attack.
#4 Controlled Use of Administrative Privileges
Attackers commonly rely on administrative privileges to carry out harmful actions within targeted enterprises. While most employees are aware of such efforts, even notoriously vigilant individuals can fall victim to scams. Common examples include opening files from malicious sites, downloading problematic attachments, or even merely visiting websites capable of exploiting users. One of the easiest to implement — and yet most effective — controls available, this step involves separating administrative accounts from personal internet activity. Additionally, systems should be configured for log entries and alerts.
#5 Secure Configurations for Hardware and Software on Mobile Devices, Laptops, Workstations, and Servers
Accessibility often plays a key role in modern software adoption — sometimes to the detriment of security. Default accounts and open services can leave organizations and their key players vulnerable. Hence, the need for this basic control, which is especially important in an increasingly BYOD (bring your own device) oriented workplace. Rigorous configuration management is essential if organizations are to keep attackers at bay.
#6 Maintenance, Monitoring, and Analysis of Audit Logs
While the cliche ‘an ounce of prevention is worth a pound of cure’ certainly applies to modern cybersecurity efforts, it’s foolish to assume that breaches will never occur. Unfortunately, even organizations with exceptional security protocol sometimes fall victim to cyberattacks. When the worst-case scenario arrives, it’s important to be prepared — not only in the interest of responding quickly and effectively, but also because a detailed understanding of one attack could potentially lead to new protocol to prevent future issues.
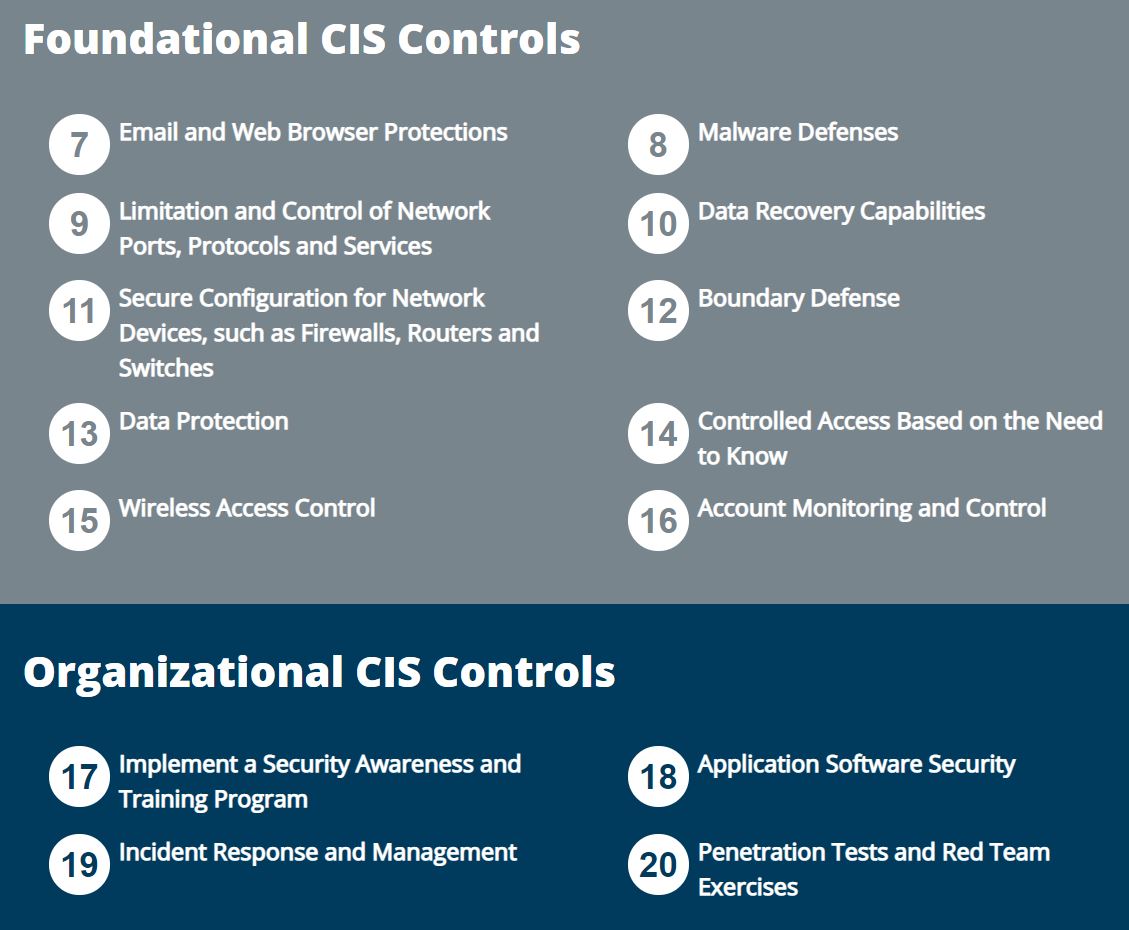 Foundational and Organizational CIS Controls (click to enlarge)
Foundational and Organizational CIS Controls (click to enlarge)
Foundational and Organizational Controls
The other control categories include foundational controls and organizational controls. These areas can help enterprises shore up their security after they have mastered the basic controls. Without mastery of the basics, however, these additional controls are not likely to serve as a viable security solution. Controls referred to as foundational or organizational include:
Foundational CIS Controls
7. Email and Web Browser Protections
8. Malware Defenses
9. Limitation and Control of Network Ports, Protocols, and Services
10. Data Recovery Capabilities
11. Secure Configuration for Network Devices, such as Firewalls, Routers, and Switches
12. Boundary Defenses
13. Data Protection
14. Controlled Access Based on the Need to Know
15. Wireless Access Control
16. Account Monitoring and Control
Organizational CIS Controls
17. Implement a Security Awareness and Training Program
18. Application Security Software
19. Incident Response and Management
20. Penetration Tests and Red Team Exercises
While there is clear value in all of the controls included on the Top 20 list, not all controls will prove accessible or applicable in all situations. Nearly all organizations, however, can benefit from implementing the controls identified as ‘basic’ by the CIS.
Comparing CIS to Other Frameworks
The CIS Top 20 is just one of several security frameworks relied upon by government and private enterprises alike. Other top framework providers include National Institute of Standards and Technology (NIST) and Payment Card Industry (PCI) Security Standards Council. While these hold clear value, they can be difficult for small businesses to adopt. The CIS Top 20 serves as an essential stepping stone for those who may feel intimidated by other frameworks or otherwise incapable of implementing them. CIS controls can also be used alongside other frameworks; some companies even use CIS standards to prioritize alternate frameworks.
Mandating Controls
Presently, the CIS Top 20 serves as a standard of care for the state of California, where the Attorney General has partnered with CIS to help local businesses follow the protocol outlined in the state’s Data Breach Report.

While CIS became a key California framework in early 2016, recent changes in the state’s privacy laws have further underscored the importance of adopting CIS controls. Signed into law in 2018 and expected to go into effect in 2020, the California Consumer Privacy Act now supplements the state’s data breach legislation, granting consumers the right to sue if breaches of data occur and businesses do not provide appropriate protection via ‘reasonable’ procedures. While the state fails to adequately define ‘reasonable’ in the context of the Consumer Privacy Act, it is clear based on previous efforts with the CIS that implementation of, at minimum, the basic six CSCs is expected.
While California has clearly set the bar high in terms of mandated internet security protocol, other state and local government entities are beginning to follow suit with similar legislation. Michigan, in particular, has made great strides in terms of encouraging implementation of prominent security frameworks. The 2018 Performance Audit Report from the Michigan Office of the Auditor General referenced NIST Special Publication 800-53 as the bare minimum regarding security controls.
In Ohio, the CIS controls are highlighted as one of a few available frameworks with which business cybersecurity practices would ideally conform. While the Ohio Attorney General maintains that the state’s recent adoption of the Data Protection Act does not serve as a minimum cybersecurity standard, it does create a valuable incentive for the local business community to amp up security efforts.
In some states, CIS controls are not yet mandated — but they are used heavily by government entities. Success at this level may eventually lead to broader mandates for government organizations and private businesses alike. As CIS experts point out, top users of the CSCs include the states of Arizona, Colorado, and Idaho. In addition to making its mark at the state level, the CIS controls are increasingly utilized in major metropolitan areas, including Oklahoma City, San Diego, and Portland, among others.
Success Stories
The Center for Internet Security offers numerous case studies that demonstrate the ability of various controls to protect against a broad range of security threats. For example, CIS highlights a top banking institution as relying on these controls for gap analysis. The banking institution’s Chief Information Security Officer explains, “If we are not quite meeting the intent of a particular CIS Control, we can identify areas to focus on and improve.” This valuable baseline has allowed the bank to maintain its status as one of the nation’s most secure financial institutions.
While the value of the CIS controls is clear in banking and finance, many retailers have yet to adopt appropriate security measures to protect their customers and suppliers. One outdoor retailer, however, is leading the way by engaging in CIS analysis not just once, but twice every year. While the retailer also uses such familiar frameworks as NIST and PCI, a top security analyst for the company explains that the CIS controls provide, by far, the biggest bang for the buck by assisting in prioritization of other frameworks. “We see the real value is in the CIS controls because they are more user-friendly and are a practical, prioritized framework.”
In another case study, CIS reveals that Corden Pharma has adopted the CSCs in hopes of meeting diverse security requirements for the company’s range of customers. Manager of IT and Business Systems John Nord explains, “[Corden Pharma] needed a more standardized security program for our company to be able to provide to our customers. The CIS controls fit that need.” Nord adds that, while initially daunting, implementation for the CSCs is not nearly as arduous as NIST framework adoption can be.
What Lies Ahead for the CIS Controls?
The CIS Top 20 are constantly evolving as new threats arise — and as new technologies become available for keeping these threats at bay. In early 2018, CIS released Version 7, which, as CIS executive Tony Sager explains, “sets the stage for future improvements in measurement, implementation, and alignment with other security frameworks.”
Although pleased thus far with the rollout of Version 7, companies are already looking ahead to Version 8. With new editions of the CSC released approximately once every three years, Version 8 can most likely be expected in 2021 or 2022. Until then, experts anticipate that states and municipalities will continue to follow California’s lead in prioritizing these security measures and working closely with CIS to ensure the adoption of robust cybersecurity controls.
Next Steps for Adopting CIS Controls
Regardless of how the CIS controls evolve in the future, it is important to get a handle on security protocol today. The widely trusted security controls from the CIS can provide a valuable blueprint. Not sure where to start? Alpine Security’s Enterprise Security Audit (ESA) service provides valuable insight into your organization’s current security protocol. Closely aligned with the CIS Top 20, this comprehensive assessment offers a holistic approach involving effective controls for cyber defense. Reach out today to discover how Alpine Security can assist your organization in adopting and abiding by the Center for Internet Security’s Top 20 Controls.











