
The Internet of Medical Things, also known as the IoMT, is one of the most revolutionary developments in healthcare today. It empowers physicians to monitor patients remotely by providing the patient with network-enabled devices. These devices can track a wide variety of processes, from medication compliance to blood glucose level.
IoMT has become an extremely profitable industry. Let’s look at the statistics:
-
87 percent of healthcare companies are using or preparing to use IoT technologies
-
63 percent of IoT technologies in use today are used for patient monitoring
-
71 percent of researchers believe that IoMT technologies are developing faster than the clinical world is ready to use them
By 2020, as many as 30 billion IoMT devices will be in use worldwide. By 2022, the market for IoMT will hit $158 billion.
The time is come to get very serious about IoMT cybersecurity.
Why IoMT Cybersecurity Is Worth the Trouble
IoMT devices offer benefits in every value metric of health care – patient outcomes, patient satisfaction, scientific advancement, and financial viability.
Lower Cost of Care
With the percentage of elderly persons rapidly increasing worldwide, experts are anticipating a potentially overwhelming rise in health care costs. The IoMT can make it possible for doctors to monitor patients remotely and send automatic recommendations when data exceeds the normal range. With this resource, doctors can lower costs by scheduling fewer in-person visits.
Additionally, because IoMT devices report data automatically, they reduce the need for nurses and support staff to verify data. This makes for more efficient use of staffing resources and focuses more attention on patient care.
Better Outcomes
Today, IoMT is most helpful in ensuring patient compliance with doctors’ instructions. An enabled device communicates data regarding outcome-related behaviors such as medication adherence or exercise habits. The same devices can track whether a patient’s condition improves or declines, thus providing key information that physicians can use to adjust care recommendations.
Customized Treatment
The pharmaceutical and medical device industries are already using IoMT to innovate around patient-centered treatment. Patients with Parkinson’s disease, for example, now have access to wearable sensors that monitor and optimize medication use to improve patients’ quality of life.
Additionally, there are numerous possibilities to add IoMT technology to pre-existing devices. For example, for patients with diabetes who use insulin pens, the IoMT could gather blood sugar data or record self-treatment schedules. The resulting data could help doctors better refine patients’ treatment plans.
Access to Research
IoMT devices allow researchers to gather vast amounts of data conveniently, thus allowing them to more easily recruit and monitor study participants. Optimizing this process benefits not only the researcher, who can spend more time with participants and evaluating results, but also the many patients who can benefit from experimental treatments.
Innovations in IoMT Technology
IoMT is going places – down a patient’s esophagus, to the grocery store, and even in a diabetic’s eye, all thanks to technology’s ability to get smaller, faster, and smarter.
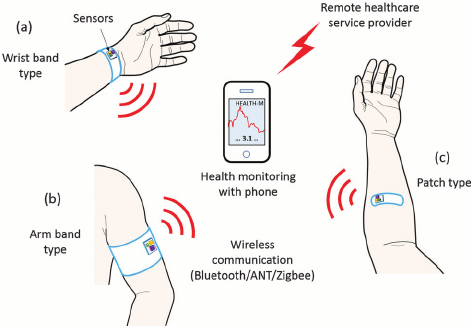 Wearable medical device examples. Image source: https://www.researchgate.net/figure/Three-types-of-wearable-sensor-nodes-powered-by-thermoelectric-energy-harvesters-The_fig1_279634036
Wearable medical device examples. Image source: https://www.researchgate.net/figure/Three-types-of-wearable-sensor-nodes-powered-by-thermoelectric-energy-harvesters-The_fig1_279634036
Wearable Medical Devices
As sensors become more advanced, device manufacturers have found ways to integrate them into wearable fabrics. This has led to advancements such as:
-
“smart” wound dressing that automates the delivery of painkillers, antibiotics, and tissue regenerating medicines
-
clothing and bedding that can alert caregivers to the needs of bedridden patients
-
bluetooth-enabled gloves that help stroke patients recover function faster
-
EEG-enhanced earbuds and headbands that improve pain management
All of these advancements help patients to get better care and take control of their health outcomes.
Ingestible Sensors
In order to increase the number of patients who take their medication according to doctor’s orders – a number calculated by the World Health Organization at just 50 percent – Proteus Digital Health has developed ingestible sensors that track when a patient has taken his or her prescribed pill. This information travels to a smartphone app so that patients and their doctors can monitor adherence.
![]() Glucose Tracking Contact Lens. Image source: https://www.engadget.com/2014/01/17/google-health-smart-contact-lenses-diabetes/
Glucose Tracking Contact Lens. Image source: https://www.engadget.com/2014/01/17/google-health-smart-contact-lenses-diabetes/
Glucose Monitoring
The Eversense XL system, distributed by Roche, uses an implanted sensor and rechargeable transmitter to send information about blood glucose levels to patients’ smartphones. Patients receive vibration alerts when glucose levels drop or rise to unhealthy levels, as well as phone notifications when levels appear to be approaching those levels. Users can also track their daily habits to understand what affects their blood sugar.
Glucose-Tracking Contact Lenses
Yes, you read that right. Google and Novartis have teamed up to create a network-enabled contact lens that measures the blood sugar in patients’ tears. The patient can view his or her data through a smartphone app and adjust insulin delivery based on results.
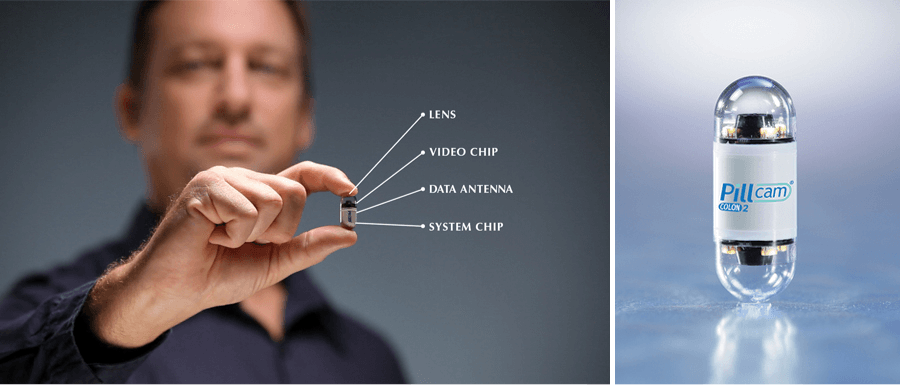 Ingestible sensor – camera. Image source: https://www.marsdd.com/news-and-insights/ingestibles-smart-pills-revolutionize-healthcare/
Ingestible sensor – camera. Image source: https://www.marsdd.com/news-and-insights/ingestibles-smart-pills-revolutionize-healthcare/
Swallowable Cameras
Doctors can now view the interior of a patient’s digestive system without uncomfortable endoscopy procedures. It happens thanks to PillCam™, a swallowable camera that provides internal views of the small bowel. As the camera travels through the patient’s system, advanced visualization technologies enable the physician to track speed of movement through the bowel and view images of potential abnormalities.
IoMT Out in the World
Not all IoMT devices are found in hospitals and laboratories. Many, like the consumer health wearables that have pervaded the consumer market, allow patients and their doctors to track health information on a day-to-day basis.
Fitness Trackers
Fitness trackers, like the well-known FitBit, are convenient wearable devices that track the body systems associated with exercise. They use:
-
bioimpedance sensors to track heart rate, respiration rate, and blood flow
-
thermometers to track increases in skin temperature
-
skin response sensors to detect sweat
-
optical heart rate monitor to measure cardiac exertion
-
accelerometers to count steps
These devices include software that can this information into health advice that the patient can use, but that’s as far as it goes. They don’t send data to doctors or recommend medications, but they do collect and store user information.
If not properly encrypted, that information could fall into the hands of hackers who might sell or alter it. There is even the possibility that a hacker could attempt to ransom a patient’s own health data back to him or her.

Smartwatch Apps
Many smartwatches now have health tracking systems that monitor the wearer’s health data. The recently-released Apple Watch Series 4, for example, tracks the wearer’s cardiac rhythm and notifies him or her if it detects any irregular heartbeats.
The watch’s Health app, meanwhile, tracks your stress levels, physical activity, sleep habits, and nutrition. These trackers can connect to a number of other third-party apps, which increases the number of companies that have access to your data.
Remote Patient Monitoring
Remote patient monitoring, also known as RPM, is one of the highest-profile trends in the health care industry.The current shift toward value-based care is making a distinct space for RPM technologies, which have the potential to reduce health care costs while improving patient outcomes and the overall patient experience.
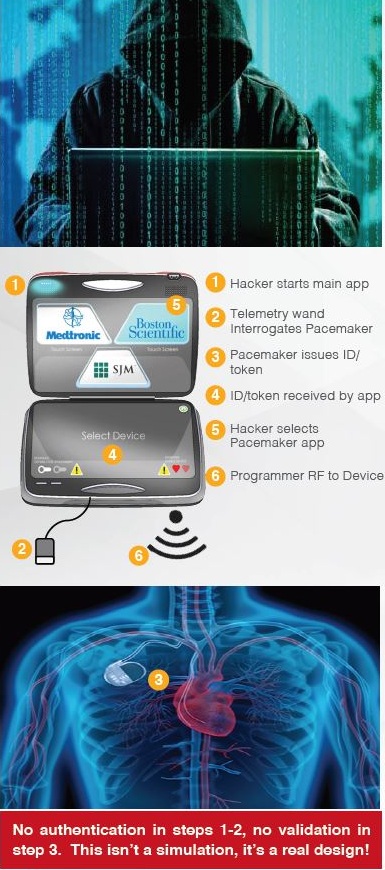 Steps to Hack a Pacemaker
Steps to Hack a Pacemaker
The Downside – IoMT Cybersecurity Concerns
Medical information is very valuable to hackers – up to 10 times more valuable than a credit card number. But it isn’t just data that cybersecurity experts fear may be at risk.
In 2012, the Showtime television series Homeland aired an episode in which a character hacked into the software that controlled the pacemaker of the US vice president. The hacker then used that access to take control of the pacemaker’s programming and caused a fatal heart attack. Shortly thereafter, then-vice president Dick Cheney’s medical team disabled the wireless feature on his pacemaker, fearing that the television program would inspire a terrorist to take similar action.
Pacemakers and cybersecurity soon dropped from the news, but they came back again just four years later.
The Pacemaker Recall
In August of 2017, the Food and Drug Administration publicized a recall of 465,000 radiofrequency-enabled implantable pacemakers after a review identified security vulnerabilities. The FDA found that a hacker could use equipment at distributed on the commercial market to gain access to the device. With this access, a hacker could change the device’s programming and harm the patient by depleting the battery or order dangerous pacing.
Fortunately, the FDA recall and development of firmware update occurred before any malicious access could occur.
 Hacking Owlet infant heart rate monitors
Hacking Owlet infant heart rate monitors
Infant Health at Risk
In 2016 in the UK, the media reported a security vulnerability in the Owlet infant heart monitor sensor. Cybersecurity researchers found that while data sent between parent smartphones and base servers was secure, the networking between the sensor and the base server had no encryption whatsoever and could be accessed without so much as a login.
That means that anyone within range could monitor the infant’s data, interfere with alert systems, or otherwise interfere with monitoring. The media deemed the situation to be the year’s worst IoT security risk.
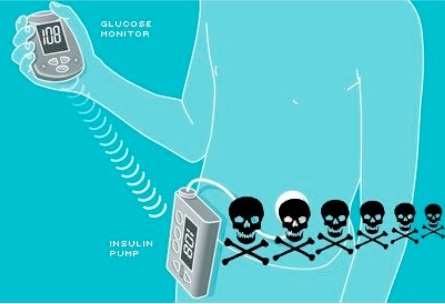 Hacking insulin pumps. Image source: https://www.extremetech.com/extreme/92054-black-hat-hacker-details-wireless-attack-on-insulin-pumps
Hacking insulin pumps. Image source: https://www.extremetech.com/extreme/92054-black-hat-hacker-details-wireless-attack-on-insulin-pumps
Insulin Delivery Made Vulnerable
All of those IoMT enabled glucose monitors? Those are vulnerable to hackers too.
In 2011, a security researcher who is also a diabetic conducted an independent investigation. He found that a hacker could intercept the signals from a glucose monitor and change the readout, which would likely cause the wearer to adjust the dosage. If the attacker repeated the process, it could prove fatal. More frighteningly, this could happen from up to half a mile’s distance.
Hackable Medication Pumps
Research has also identified vulnerabilities in a particular brand of infusion pump, a type of technology that delivers medication into patients’ bloodstreams. In 2014, an independent professional reported that he had written a program that could instruct pumps to deliver lethal doses of medicine. The researcher found these vulnerabilities in at least five pump models.
Whole Systems at Risk
IoMT devices also put the hospital at risk of what is known as a backdoor attack. In one well-publicized example, hackers used malware to infect blood gas analyzers, which are important for the monitoring of critical care and surgical patients. The infected devices allowed attackers to infiltrate hospital networks and extract confidential data, which was then sent to an undisclosed European location.
A simulation of the attack revealed that the blood gas analyzers were routinely sending unencrypted data. That meant that the hackers could make any changes that they wished within the hospital system – to patient data, to treatment and diagnostic requests, and even to key administrative information.
Identifying Key Vulnerabilities
The IoMT would be a vulnerable situation even with adequate safeguards in place, simply because it sends and receives extremely personal information. Unfortunately, most of today’s systems are not set up to protect such private data.
Outdated Software
Some working medical devices, such as CT scanners and even pacemakers, are upwards of 20 years old. These devices are capable of connecting to hospital systems but feature software systems that have not been conscientiously updated. Such systems are not set up to defend against today’s advanced threats, which can disable an entire hospital network through a single device.
Departments Working in Isolation
In order for medical devices to be truly secure, all stakeholders must participate in screening for and responding to threats. This can be a difficult task in a complex healthcare organization where the primary focus is typically the immediate health of the patient.
The clinicians who use these devices often have so many pressing patient care tasks that they can easily overlook cybersecurity updates Meanwhile, facility IT staff and device manufacturers become involved with their own team’s tasks.
This isolated way of working does not stand up to the complex and interlocking demands of medical device cybersecurity. In order to defend systems and devices from intruders, stakeholders must come together to create a unified security strategy.
Unclear Regulations and Poor Compliance
Manufacturers and healthcare delivery organizations (HDOs) have traditionally lacked clear mandates regarding the security of medical devices. A 2017 survey revealed that just 44 percent of HDOs and 51 percent of device manufacturers followed FDA guidelines to make devices more secure, despite the fact that approximately 33 percent of both groups were aware of potential harm to patients if a security breach did occur.
Improving Security and Protecting Patients
In one of the first major steps toward improved monitoring of cybersecurity, the FDA recognized the UL 2900 standard for medical device cybersecurity in August of 2017. Officially published as UL 2900-1, the standard offers a series of checks designed to identify vulnerabilities.
By recognizing the standard, the FDA enables manufacturers to indicate UL 2900-1 compliance as a response to cybersecurity concerns.
Regulatory Updates
In late 2018, the FDA published draft guidelines that bring medical device cybersecurity requirements up to date with today’s risk set. Changes include:
-
A two-tier risk assessment system that prioritizes devices with the ability to connect with other products, a network, or the Web
-
Mandated documentation specific to a device’s or system’s risk tier
-
A Cybersecurity Bill of Materials (CBOM) that lists software and hardware with potential vulnerability to hackers
-
Greater alignment with the National Institute of Standards Technology’s globally acknowledged Cybersecurity Framework
The FDA hopes that aligning with the Framework will improve UL 2009-1 compliance.
Recommendations, Not Mandates
The released documentation is geared toward premarket submissions and “contains nonbinding recommendations.” It is yet to be seen whether these recommendations are compelling enough to increase the percentage of manufacturers and HDOs that are actively trying to prevent attacks, a percentage most recently measured at 17 percent and 15 percent respectively.
Recommendations for HDOs
In 2018, the FDA collaborated with government research contractor MITRE Corp. to develop a cybersecurity guide for medical devices. The guide provides recommendations for healthcare providers and other involved organizations to prevent and respond to cybersecurity incidents involving medical devices. It features such recommendations as:
-
Creating a threat detection standard for all of an enterprise’s devices and networks
-
Investment in firewalls and other prevention technologies
-
Inventorying of an enterprise’s full range of medical devices, with attention to those with connectivity capabilities
The latter plays a particularly important role in uncovering security vulnerabilities. Only by identifying areas of potential risk can a provider screen for and correct vulnerabilities.
Next Steps for Attack Prevention
Technology never stays still and neither do hackers. The new developments in protecting patient data and patients themselves will not be the end of healthcare cybersecurity, nor will they guard against every possible way of hacking IoMT devices.
It is vitally important for all HDO’s to develop and implement medical device security and IoMT security strategies. These strategies need to include not only a screening and threat mitigation standard for current devices but also a plan for maintaining security on a continuing basis.
Simplify Clinician Processes
Clinicians, both doctors and nurses, have their hands full with patient care. Any cybersecurity tasks, such as authentication checks, must be minimal on their part and automated as much as possible. Software updating and other processes must not disrupt workflow.
Threat Mitigation Training
The concept of keeping the clinician involved but uninterrupted also applies to threat intervention strategies. All personnel involved with a device or network must know what to do if a data compromise occurs.
Network Segmentation
Many security experts are now advocating for increased segmentation of enterprise systems. By segmenting their networks, organizations can more effectively implement security checks and isolate any threats before they pose a widespread risk.
Encryption of Patient Information
Because IoMT devices expose more patient information to enterprise networks, it is important for electronic health records (EHRs) to be as secure as possible. Technology such as homomorphic encryption, which secures data even as it is being used, can keep patient information safe from unwanted access. Protection can even be applied to personally identifiable information (PII), which is particularly valuable to cybercriminals.
Investing in Prevention
An ounce of prevention is still worth a pound of cure, both in patient care and in IoMT cybersecurity. As much as possible, security analytics and software updating should be automatic. The most critical and complex tasks can be passed on to a third-party provider with expertise in medical device security and the hacking of IoMT devices.
The FDA has placed the burden of IoMT cybersecurity on the people who develop and use them. This adds a set of high-urgency tasks for companies that are already tasked with the safety and well-being of patients. It is unsurprising that experts urge companies to outsource high-level tasks to a company with the expertise to handle them.
Alpine Security provides penetration testing services with a focus on IoMT devices. Through extensive experience in ethical hacking and identification of cybersecurity risk, we can relieve HDOs and manufacturers of the necessary burden to review and test all enabled devices, freeing those organizations to focus on patient outcomes.



